Is the inter-Korean conflict going cyber?
South Korea blames the North for cyber attacks while questions remain over how such an IT powerhouse was left vulnerable

South Korea has one of the most advanced IT infrastructures on the planet, offering the world’s cheapest access to the fastest internet connection anywhere. Approximately 95 per cent of its near 50 million citizens surf the web – a statistic virtually unmatched by any other country.
Despite being so technologically advanced, however, the country continues to suffer from ongoing cyberattacks, which authorities say are from North Korea.
Keep reading
list of 4 itemsRare deep-sea squid filmed by scientists
Palestinian life under Israeli occupation: An illustrated guideThis article will be opened in a new browser window
Boeing’s jets turn 70: A timeline of highs, lows and turbulence
Seoul has identified the assaults as part of the North’s plans to strategically nurture its cyberwarfare unit, and responded with pledges to bolster its own cyberdefence programme by doubling its number of hackers. It is also establishing 24-hour cybersecurity centres under the auspices of key government agencies such as the unification ministry and the central bank.
South Korean authorities and experts, alongside defectors from the North say the country’s communist neighbour may be taking its war with the South from the trenches to the cybersphere – seeing it as a more effective way to topple its capitalist enemy.
The two Koreas remain technically at war, since they never signed a formal peace treaty to mark the end of the Korean War, which began on 25 June, 1950.
But critics say the elusive nature of such hacking incidents makes it impossible to know for certain that the North was behind these assaults – especially considering the reclusive country’s perceived lag in technological advances as a result both of its self-isolation and from years of sanctions imposed to pressure Pyongyang to give up its nuclear weapons.
Fielding attacks
Over the past several months, some 60 cadets and officers of South Korea’s prestigious military academy have received emails with the subject line: “It’s me, a fellow alum”, and “I miss you, buddy!”.
The body of the emails contained information that was specific to the academy, such as jargon often used by cadets and references to specific campus locations, making it hard to believe that the emails were written by anyone who was not affiliated with the academy, a cadet told Al Jazeera on condition of anonymity, citing military policy.
This month, South Korea’s defence ministry announced that North Korea had been distributing emails to cadets and officers of the Korean Military Academy designed to hack into the institution’s computer system.
A ministry spokesman refused to give additional details as to how it verified that the North was responsible or how such a massive security breach was attemped, only proffering information on how the ministry had since taken appropriate measures “to handle the situation”.
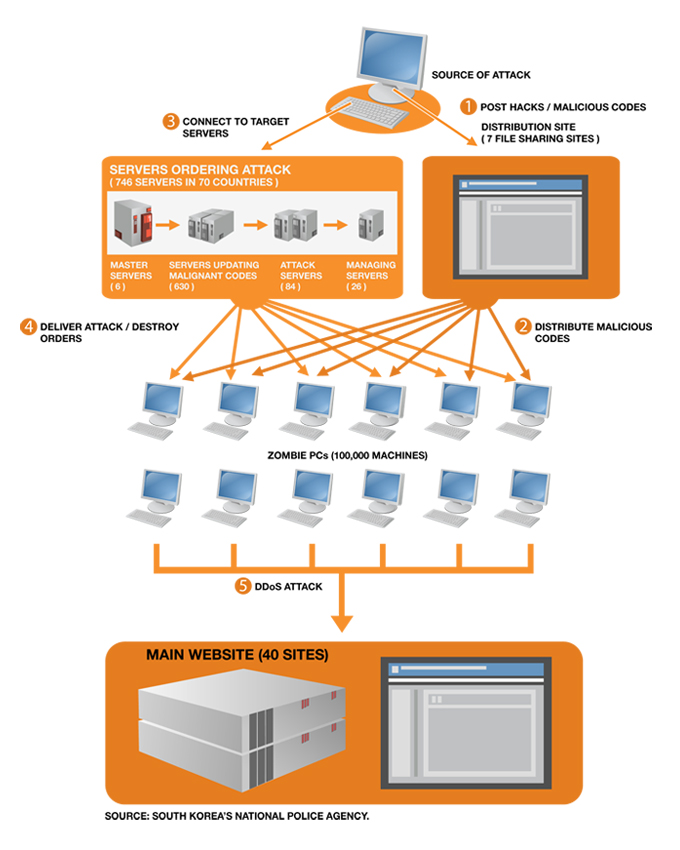
In March, 40 South Korean websites, including those of the presidential office, the National Intelligence Service and the defence ministry, were targeted for three days in Distributed Denial-of-Service (DDoS) attacks, where malicious codes flooded the networks with fake access requests, causing them to crash. In April, more than 20 million South Koreans lost access to their accounts at the National Agricultural Cooperative Cooperation, more commonly known in Korean as Nonghyup Bank. Global positioning system (GPS) signals have also been periodically jammed, affecting cellular phone service for civilians and troops in Seoul.
Authorities in the South have blamed North Korea for each of the assaults.
Prosecutors and the National Police Agency (NPA) concluded in May that the method of the March and Nonghyup cyberattacks was exactly the same as in 2009: a malicious code was distributed through peer-to-peer file sharing sites, transforming personal computers that downloaded the files into “zombie computers” that performed the DDoS attacks.
In October 2009, Won Sei-hoon, head of South Korea’s National Intelligence Service, testified to lawmakers that the top spy agency had identified the culprit of the July attacks as North Korea’s Ministry of Posts and Telecommunications, after tracking the source of the attacks to a location in China occupied by the ministry.
“There are over 4.2 billion internet protocol (IP) addresses in the world, and it would be impossible for the latest attack to be initiated by a different hacker because it used the same IP address as in the 2009 DDoS attack,” the Cyber Terror Response Center said.
DDoS: simple but complicated?
Pyongyang has denied all charges and accused Seoul of inventing a conspiracy to fuel confrontation.
Much criticism has risen in South Korea questioning how a leading information technology powerhouse was left vulnerable to cyberattacks by an impoverished nation in serious economic and food crises.
Some South Korean computer experts have voiced doubts over the government pinpointing Pyongyang as the culprit, saying that evidence was too “weak” and only based on “circumstantial assumptions”.
Haroon Meer, a cybersecurity expert and founder of Thinkst Applied Research, says DDoS attacks aren’t a result of sophisticated technology, but rather “a [matter of] brute force”.
 |
Meer also calls DDoS attacks a “minor” and “quantifiable problem”, likening it to an annoying “road block on a busy road”, and warned of more serious cyber “weapons” like Stuxnet, a worm that is reported to have set back the Iran’s nuclear programme by more than two years.
“A DDoS attack kind of exists for as long as [the attacker] is existing … but once an attack like Stuxnet happens, it compromises your core and internal for so long, so it compromises what you can trust of your machines,” Meer said.
“[DDoS] is a road block on a busy road, which is not as bad as someone destroying the road forever or shaking confidence in people to ever use the road again, or someone affecting our computer and planning, and build insecurity [within us] in going forward.”
“In the [range] of weapons, for me, [DDoS] is really a primitive one that I won’t be spending my time worried about,” he added.
But one South Korean computer engineer operating in Silicon Valley says the very simple and primitive nature of DDoS attacks is what makes it so threatening.
“There lies a big challenge in distinguishing between regular increase in traffic to the targeted website with the flooding of DDoS requests aimed at crashing the target’s server,” the engineer told Al Jazeera on condition of anonymity due to sensitivity of the issue.
‘Internet black hole’
North Korea ranked last in a 2011 survey of threats to independent media in 196 countries and territories carried out by Freedom House, an independent watchdog organisation that supports the expansion of freedom around the world.
The North has been aptly called the world’s “worst internet black hole” as the country’s 24 million do not have access to the World Wide Web.
North Koreans can only publicly access Kwangmyong, the nationwide intranet established around 2000 by the Pyongyang-based Korea Computer Center, which connects universities, libraries, cybercafes and other institutions with websites and email.
“It’s like broadcasting material from a centralised source, which people can download, and that is the only source of communication for the North Korean public,” Kim Heung-kwang, a defector who was a computer science professor in North Korea, told Al Jazeera.
Full access to the web is limited to a few thousand North Koreans – an estimate given by academics Cheng Chen, Kyungmin Ko and Ji-yong Lee in a December 2010 report for the Pacific Review.
Culpable or capable?
How is a country that lacks general infrastructure and public access to the internet able to carry out cyberattacks on IT powerhouses such as South Korea and the US?
“Contrary to popular belief, there was a time when North Korea was once a global leader in information technology,” Kim Heung-kwang, the former North Korean professor who defected to the South in 2004, told Al Jazeera.
Kim says Kim Il-sung, founder of North Korea and father of current leader Kim Jong-il, began investing in information technology in the 1960s.
Until the late 1970s, the North had benchmarked the technology to develop hand-made “minicomputers”, the first generation of computers which were, ironically, huge machines that filled rooms. After Intel developed the microchip in 1978, which essentially minituarised such computers’ functions into a chip the size of a finger nail, North Korea lost standing in hardware development, lacking the funds to stay ahead in the game.
But, in the realm of software development, the North has managed to be somewhat competitive, as the technology is based on excellence in application of mathematics and basic science.
“So when you ask how can a lagging country like North Korea be so good at hacking, I want to say that you’re looking at a technology that they’ve been honing for the past 50 years,” Kim told Al Jazeera.
However, in addition to its lack of untrammeled access to the internet, North Korea does not have routine access either to advanced technologies, or to reliable electricity supplies. It is also reliant on China and Japan for internet hosting services and would be not be able to “use the proxy strategy followed by both China and Russia, where private hackers carry out state instructions, operating as irregular forces or mercenaries”, said Kim.
Marcus Noland, deputy director and senior fellow at the Peterson Institute for International Economics, says these motives are consistent with the country’s governing Juche [“self reliance”] ideology and its control over the economy.
“It is a common theme in North Korean economic discourse to emphasise scientific breakthroughs and technological developments. The reason is that it is a way of offering some hope or rationale for prosperity, without confronting the systematic deficiencies of the economic system of the regime,” Noland told Al Jazeera.
“The North Koreans are regularly going on about science and breakthroughs because it allows them to not talk about the fact that the effort to centrally orchestrate their economy has been a failure.”
While reports about the isolated North grooming computer prodigies to become hackers for its bolstered cyber warfare programme cannot be independently verified and thus “must be taken with a grain of salt”, Noland believes there is “some truth” to the North being capable of cyberattacks such as those that have recently hit South Korea.
“Cyber responses to the South Korean conventional forces’ superiority is consistent with basic discussions and tendencies in economic sphere for decades,” Noland told Al Jazeera.
“In order to provide, in their minds, for the political security of the regime, they have to have other non-military capabilities to threaten South Korea. It costs a lot of money to procure weapons of mass destruction and [their] delivery systems. It’s a country that cannot compete in terms of putting tanks on the field and are trying to maintain some kind of capacity to deter an adversary,” he said.
Repercussions for the internet
Haroon Meer, the cyber and information security expert, says governments must be careful when attempting to enforce regulations that infringe upon online freedoms, and should first look into technological approaches to achieve better security solutions.
“One of the fundamental problems that you’re going to get to is that our technology is immature. You’re seeing a fundamental problem with the internet: such attacks are technically possible right now and [for the moment] it’s easier to be a offender than a defender,” Meer said.
“All the talk of cyber war is going to get people to usher in regulation that can start to affect our freedoms on the internet because that will become a way to protect, for which we haven’t had ways to protect technologically.”
The Silicon Valley engineer also pointed to a more fundamental problem with the lack of better cybersecurity: the fact that cybersecurity experts don’t see the need to invest in defence mechanisms – unless a need for them arises.
“It seems that the industry puts emphasis on finding ways to securely send and receive information, rather than network security,” the engineer said.
“For now the only way to prevent DDoS attacks and hacking incidents at large is to stop hackers from accessing the internet, but there is no actual way of doing that,” he said.
“Even if that were possible, that would undermine the very raison d’etre of the internet – an egalitarian tool for communicating and exchanging information.”
Follow Sangwon Yoon on Twitter: @sangwonyoon