‘Professional hacking’ company suffers data breach
After being hacked, Italian software surveillance company accused of selling malware to states accused of rights abuses.
An Italian software surveillance company has been accused of designing and selling malware to countries accused of human rights abuses, after it suffered a data breach of its own.
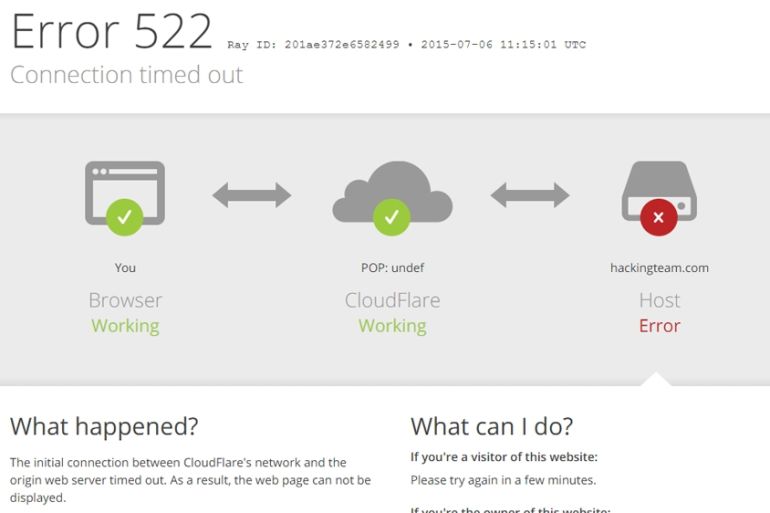
Hacking Team suffered the security lapse late Sunday evening according to a report by CSO Online , a news and analysis website focusing on information security.
Keep reading
list of 4 itemsCould shipping containers be the answer to Ghana’s housing crisis?
Are Chinese electric vehicles taking over the world?
First pig kidney in a human: Is this the future of transplants?
The report said 400GB of information, including emails, had been leaked, allegedly revealing transactions with the intelligence agencies of countries including, Russia, Egypt, Uzbekistan, and Kazakhstan, among other states.
CSO said the invoices revealed in the leak totalled almost $4.5m.
.@HackingTeam hacked: documents show company sold exploits and spyware to UN-blacklisted governments https://t.co/0eJCOsscJW
— Anonymous🍏 (@YourAnonNews) July 6, 2015
Christian Pozzi, a member of Hacking Team, defended the company on Twitter against the accusations made against it, but his account was also hacked and subsequently taken offline.
“Don’t believe all the false info [sic] the attackers are spreading, anyone can create adult links and upload them,” Pozzi said, responding to criticism by online activist group Anonymous.
“We don’t create viruses, we simply create custom software solutions. Stop spreading lies about the services we provide,” Pozzi said in another post on Twitter.
Reporters Without Borders (RSF) lists Hacking Team as one of its “Enemies of Internet” , for selling encryption breaking software and Trojan viruses to Morocco and the the UAE, allowing those countries to monitor VOIP applications like Skype and spy on journalists.
I hope whoever popped @hackingteam also drops a list of those targeted and exploited. Especially the journalists and human rights activists.
— Jacob Appelbaum (@ioerror) July 6, 2015
RSF quotes the company’s mission statement on its website before it was hacked.
“We believe that fighting crime should be easy: we provide effective, easy-to-use offensive technology to the worldwide law enforcement and intelligence communities. Technology must empower, not hinder,” the statement read.
Trojans are a form of malware that can be placed on a user’s computer or smart phone without their knowledge.
Although they serve a number of functions, including disrupting services on a device, they can also be used to monitor and relay information to those who have installed it.