Cracking down on cybercrime in Ivory Coast
Ivory Coast tackles internet fraud scourge, but analysts say criminals continue to outsmart authorities.

Abidjan, Ivory Coast – At 6:30am more than 20 men aged between 14 and 28 – mostly school dropouts – gathered in front of the metal door of a street-side shop waiting for it to open.
After a few minutes, a weary fellow in his late 30s trudged down holding a thick bunch of brass keys and undid the padlocks, ignoring taunts about his hangover from the crowd behind him. When he pulled the door open, the men surged inside to snaffle the few desktop computers.
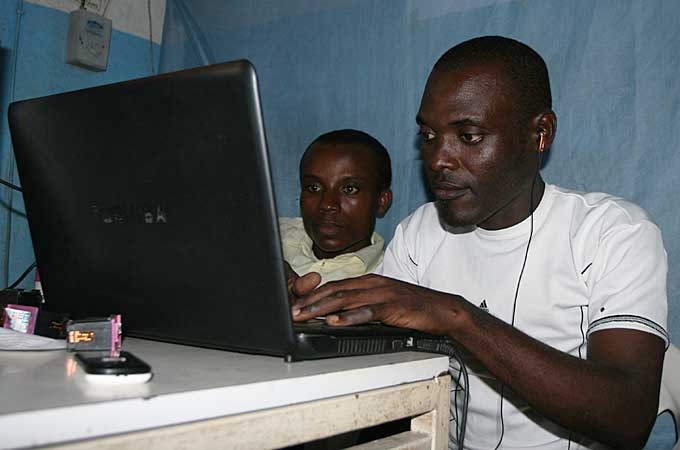 |
| Dropouts are learning how to use different computer applications but decline to reveal what for [Kingsley Kobo/ Al Jazeera] |
“They stay here everyday until 10pm when I close. Some do not even go out for food or drink for fear that someone else will take their seat. They call their girlfriends to bring them snacks and soft drinks,” says Jean Luc Tiemele, who runs the stuffy, one-room internet café mainly patronised by dubious youth, known colloquially in Ivory Coast as “Brouteurs” – or grass eaters.
Keep reading
list of 4 itemsHong Kong’s first monkey virus case – what do we know about the B virus?
Why will low birthrate in Europe trigger ‘Staggering social change’?
The Max Planck Society must end its unconditional support for Israel
“For me I don’t really know how they proceed, but I see that they harvest thousands of email addresses per day using diverse apps and send countless emails of business proposals to those addresses.
“Once they get a response, they follow it up until that person pays up some money, which they in-turn squander on girls, expensive mobile phones, wristwatches, perfumes, drinks and sometimes cars,” Tiemele says.
The story is the same at almost every internet café in the main Ivorian city of six million inhabitants, with thousands of small and large computer halls for public use, which locals say have been seized by cybercriminals, who spend seven days a week in front of computer screens seeking fast cash.
“You can’t find any cybercafé in Abidjan without these rogues,” says Armand Zadi, founder of Internet pour l’Avenir, or Internet for the Future, an NGO that campaigns against abusive use of the internet in the West African country.
“They have abandoned schooling and believe they can succeed in life through internet scams because they see other young men in town who make money from it and later branch out into legitimate businesses. Our fear is growing that they could become role models for other youths,” he says.
Consequences and reactions
The Ivorian government has set up a special forensic police unit, Plateforme de Lutte Contre la Cybecriminalité (PLCC). It is composed of policemen, computer and telecommunication experts, and law practitioners to combat escalating cybercrime – which analysts say has dented the image of the country abroad.
Annual reports published by the PLCC showed that victims lost $6.2m in 2012 and $6.6m in 2013 from cybercrime carried out in Ivory Coast. A total of $28m has so far been stolen since the police unit began keeping records of complaints five-years ago.
It's a serious menace to our economy, to our reputation as a safe place to invest and even to our tourism industry.
If nothing vigorous is done, the rising scourge could scare away foreign investors and blacklist the world’s largest cocoa grower, according to PLCC chief Guelpetchin Moussa Ouattara.
“It’s a serious menace to our economy, to our reputation as a safe place to invest, and even to our tourism industry,” Ouattara says.
“And mind you, many locals feel victims are only people from the West, but our 2013 report shows that Ivorians are increasingly becoming victims. So this is a very serious situation that we are bent on tackling.”
The PLCC received 514 complaints from victims in 2013, 42 percent of which came from locals, and arrested 50 suspects who were prosecuted.
Nearly half of the victims were conned in romance scams, according to the police report, while phishing scams represented 10 percent, and identity fraud seven percent.
Ouattara says more suspects could have been brought to book. “We can‘t arrest anybody we see in front of a computer. My team respects human rights. We only proceed to bust once we have fully investigated.”
The use of fake identities, pseudonyms, and phone numbers by cyber rogues bedevils police sleuthing, says Ouattara. “We have to use other methods … including telephone data to trace these guys, which may take months, or up to a year.”
In 2012, all mobile phone companies and internet service providers in Ivory Coast were asked to identify their customers to enable traceability. According to the telecommunications agency ATCI, which regulates the sector, more than 17 million mobile phone users have so far been registered, representing 92.8 percent of total subscribers in the country of 22 million people.
Previously there was no legal basis to prosecute internet fraudsters, but the government in 2013 signed into law two bills against cybercrime and the protection of personal data. Penalties are from one month to 20 years in prison, and fines are between $1,000 and $200,000.
Various victims
Swiss and French police have collaborated with the PLCC to uncover numerous phoney transactions, leading to the arrest of a dozen young men and women in Ivory Coast. One of the victims, who is based in Switzerland, tells Al Jazeera that he lost much of his life’s savings in an Ivorian scam.
I kept sending funds to her for one thing or the other until I finally realised she was a man and had been defrauding me.
“First it was a simple email I found in my inbox. She was telling me of business opportunities in the Ivory Coast and how she could help me get a cheaper and faster licence to operate in the country,” Steve Widmer says.
“She even sent some money [to me] for DHL fees to send my documents faster so she could submit them with her uncle at the ministry of commerce, which I did. The whole thing took more than a year and we later became good friends even without meeting each other.
“I kept sending funds to her for one thing or the other until I finally realised she was a man and had been defrauding me,” he says.
Sylvie Kouassi, a 37-year-old Ivorian businesswoman, says she lost $4,200 to fraudsters in Abidjan when she opened her email at an internet café to organise funds wired from abroad.
“I was told the money had been cashed when I went to a money-transfer agency for withdrawal. I later discovered the computer I had used at the café was infected with spyware,” she says.
Brouteurs install diverse spyware on computers at internet cafés to retrieve passwords and email addresses in order to check for fund-transfer codes and other usable information, according to Silvestre Moke, an internet security engineer at Stamteck in Abidjan.
“The safest thing to do is never going to a public café to check an email account. They could monitor your inbox for days and even months without you knowing,” he says.
Colonial debt
“Cybercrime in Africa is not really a crime, it is known as colonial debt. The Whites are paying us what they stole from our forefathers and what they continue to steal from our rich soil,” a 25-year-old cybercriminal boldly says, refusing to give his name for fear of police reprisals.
“It’s true some locals are falling into our trap, but our main target is people from the West. We don’t have jobs, banks don’t give us loans for business, what else do you expect us to do to survive? In the past, our elder brothers used to travel to Europe to seek greener pastures, but embassies no longer give visas. The internet is just another chance for the African youth,” he says.
Nearly every cybercriminal in Ivory Coast uses the “colonial debt” theme as a pretext. It has also inspired a popular song released in 2012 by a local anti-imperialism artist titled “Dette Coloniale”.
Lately, however, the growing awareness of internet fraud is hampering business for the rogues, who say people are becoming too careful to fall into their net.
As authorities step up efforts against high-tech trickery, the rogues are thinking up cleverer methods to elude controls, with no end in sight to the phenomenon.